RISE OF CYBER CRIMES- THE NEED FOR INVESTIGATION AUTHORITIES TO BECOME TECH SAVVY
- brillopedia

- May 30, 2021
- 9 min read
Author: Ayushi. R, IV year of B.Com.,LL.B(Hons) from The TamilNadu Dr. Ambedkar Law University, School of Excellence in Law, Chennai.
Co-author: Balaji AP, LL.M from Government Law College, Villupuram.
ABSTRACT
“For every lock, there is someone out there trying to pick it or break in”.
Cybercrime is the biggest threat these days with the development and access to technology across the world. Moreover, rapid advancements in information technology constrained the ability of adapting the existing laws or creation of new laws to regulate the cyberspace.
Furthermore, the investigating agencies of our country must be well-equipped to tackle such heinous crimes. Thus, the paper will elaborately explain the nature and effects of the cybercrime. Before proceeding towards the main issue, the paper will discuss the meaning and scope of cybercrimes. In the next stage, the research will be focused on a few key points of the MacAfee Report along with the statistical data regarding the cybercrimes in India.
Further, the paper will enumerate the role of investigating agencies in tackling such issues and provisions with respect to cybercrimes provided under the Information technology act, 2000. Finally, the article will shed light upon a few guidelines given by The Supreme court and Indian police Journal regarding the same along with the cases of S.M Balaji v. State & Subhendu Nath v. State of W.B., for explaining the practical situation in tackling such issues.
KEYWORDS: CYBER CRIMES, INVESTIGATION, CYBER FORENSICS
INTRODUCTION
“Information is the oxygen of the modern age. It seeps through the walls topped by barbed wire; it wafts across the electrified borders.” -Ronald Reagan
In modern times, India has become the most important region for cybercriminals, where most intruders and other vindictive users commit crimes through the internet.
The Internet today has become a substitutable form of life and living due to the increasing dependence and reliance of human beings on these technologies. As a result, humans are now proficient in doing things which were unimaginable previously. Whereas, on the other hand, the huge widespread of the Internet and computer technology universally has given rise to Cyber Crimes. It has escalated in rapid strides because of the quick diffusion of the Internet and the digitisation of economic activities.
Therefore, to explain the above issue in detail, the paper will elaborately explain the nature and effects of cybercrimes. In the next stage, the research will be focused on a few key points of the MacAfee Report along with the statistical data regarding cybercrimes in India. Further, the paper will enumerate the role of investigating agencies in tackling such issues and provisions with respect to cybercrimes provided under the Information technology act, 2000. In the last stage, the article will shed light upon the case of S.M Balaji v. State depicting the practical situation in tackling such issues.
DEFINITION OF CYBERCRIME
There is no proper definition of Cybercrime provided by The Indian Legislature in any statute. The Information Technology Act, 2000, which deals with cybercrime, has not defined the term “cybercrime”. However in the usual sense the term cybercrime denotes any illegal activity which is carried over or with the help of the internet or computers.
According to Black’s Law Dictionary, a Crime that takes place through the use of computers, computer technology or the Internet is known as cybercrime. In simple terms, it refers to all the activities done with criminal intent through the medium of the internet (Pavan Duggal).
Therefore, any activity which basically offends human sensibilities can be included in the ambit of cybercrimes.”
Further, CYBER CRIME INCLUDES:
Email spoofing
Hacking
Phishing
Cyberstalking
Cyber defamation
Cross-site scripting
Vishing
Cyber trafficking
Web jacking
Malicious Software
SMS Spoofing
IMPACT OF CYBER CRIMES
Humans today are favourably dependent on computers and the internet/online mode for money transfers and making payments. Hence, the risk of being exposed to online money frauds is exceptionally high. In 2011, according to Norton Cybercrime, over 74 million people in the United States were victims of cybercrime in 2010, which directly caused financial losses of approximately $32 billion.
Even in India, with the advent and popularity of “cashless India”, chances of being conned through online transactions are also rising if one is not clever enough to use safe online transaction platforms and applications. Moreover, it is not just individuals who are suffering from the financial crisis because of cybercrimes, certain surveys conducted have indicated that approximately 80% of the companies joining in the surveys admitted financial crisis due to cybercrimes.
Also, as per the Delhi Police reports, almost 135 cases of cybercrime were reported every day in May, making it a total of 4,188 cases in May and around 33,000 reports till November were recorded. Therefore, it was evident that the rate of cybercrime was high during the lockdown period. Further, to explain this point more elaborately, the research has also been focused on the MacAfee Report of 2020.
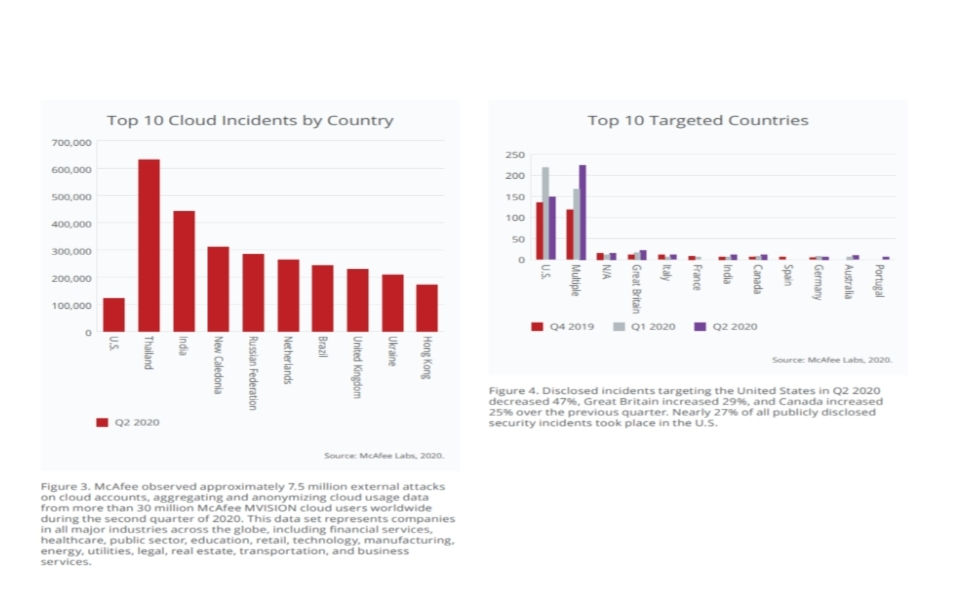

The above report predominantly discusses how drastic the increase of cybercrimes is and their impact on the economy.
PARALLEL PROVISIONS UNDER THE INDIAN PENAL CODE AND INFORMATION TECHNOLOGY ACT
Many of the offences penalised by the IPC and the IT Act have similar ingredients as well as nomenclature. Here are a few examples:


PRO-ACTIVE MEASURES TAKEN BY THE JUDICIARY TO RAMP UP THE SKILLS OF INVESTIGATING OFFICERS IN CYBER CRIME CASES
With the growing impact of technology in daily life, and as a result, the production of electronic evidence in cases has become relevant to establish the guilt of the accused or the liability of the defendant.
Therefore, electronic documents stricto sensu are accepted as material evidence. Moreover, the linking of science with traditional criminal investigation techniques requires new perspectives in the criminal investigation. These new perspectives in the investigation rather place reliance upon a skilled scanning of the crime scene for physical evidence than informers and custodial interrogation.
Further, it is evident from the graphical representation shown in the previous chapter that cybercrimes are increasing rapidly, and there is an absence of awareness as well as readiness in the police force to deal with such crimes. Thus, there is a crying need to train and acquaint members of the police force in the matter of collection, reception, storage, analysis, and production of electronic evidence in court in accordance with the procedure stipulated under law.
Also, the Madras High court in one of its recent judgement clearly stated that “Cyber crimes have reached monumental proportions and criminals committing these offences are clearly having the upper hand since these criminals are intelligent crooks and police officers require regular training and exposure to tackle these crimes.” A comprehensive structure is mandatory to enhance the quality of the investigation.
Adding on to the above judgement, the Apex court in Kishore Chand v. State of H.P also observed the duty of the state and investigating agencies in tackling such issue and held that “It is time that the investigating agencies evolve new and scientific investigating methods, taking aid of rapid scientific development in the field of investigation. It is also the duty of the State, i.e. Central or State Governments and the Judiciary, to keep the investigating officers abreast of the latest scientific development in the art of investigation and the march of law so that the real offender would be brought to book and the innocent would not be exposed to prosecution.”
Further, The Sixteenth Law Commission (Maliamath committee), in its 185th Report submitted in 2003 had proposed the use of Forensic Science and modern technology in investigations right from the commencement of the investigation and creation of a cadre of Scene of Crime officers (SOCO) for the preservation of scene of crime evidence and collection of physical evidence, for better use of technology for fighting crimes.
The importance of electronic evidence in cybercrimes is again discussed in the following manner:“It is also relevant to note that electronic evidence by its very nature is susceptible to tampering and/or alteration and requires sensitive handling. A breach in the chain of custody or improper preservation of such evidence renders it vitiated, and such evidence cannot be relied upon in judicial proceedings. Thus, any lacuna in that regard would render such evidence vulnerable with regard to its probative value.
GUIDELINES/RECOMMENDATIONS/SUGGESTIONS
For the said purpose, certain directions were issued by the Calcutta High court to ensure that investigation of crimes involving electronic evidence is conducted in a fair, impartial and effective manner.
They are:
Proper training of members of the police force in reception, preservation and analysis of electronic evidence.
Only the officers who have been trained in accordance with the manner as stated above shall be involved in the investigation of crimes involving offences under the Information Technology Act, 2000 and the offences in which electronic evidence plays a predominant part.
Every district shall have a cyber cell comprising of officers with specialized knowledge in the matter of dealing with electronic evidence in assisting the local police.
A standard operating procedure regarding preservation, collection, analysis and producing electronic evidence to be submitted by the Director-General of Police, West Bengal on the next date of hearing.
Specialized forensic units to be set up in the State in order to facilitate examination and/or analysis of electronic evidence.
Further, A Heterogeneous committee was also constituted by the Madras High Court to give its recommendations on
A) Reforms that can be brought into practice for reformation, rehabilitation and reintegration of the convict/accused person into society and
B) Best practices for improving the quality of investigation.
But this was subsequently set aside by the Supreme Court owing to the lack of jurisdiction on the part of the High Court.
Similarly, the Apex court and the Indian Police Journal issued a few guidelines/procedures which are to be followed by the Police officers/Cyber forensic experts while dealing with the electronic evidences under section 65B of the Indian Evidence Act, 1872,
a)The admissibility of a computer output as an electronic record depends upon the production of a certificate/statement that the computer output satisfies the four conditions under section 65B (2) of the Indian Evidence Act.
b)Observing the difficulty in describing how the statement was produced and mentioning the configuration of all the devices involved in the production of the electronic record by the computer, the Hon’ble Supreme court has observed that such a certificate is “not mandatory” in certain exceptional cases. Further, the forensic experts should treat this “not mandatory” clause only as “certain pieces of information are not mandatory in the certificate” and not as “the certificate itself is not mandatory”.
c)Although there is no legislation or precedent regarding forensic protocols, processes and procedures which are to be abided by the cyber forensic experts, it is necessary that the experts must include certain important details such as:
The nature of the electronic evidence presented by the forensic expert.
Details of the geographical location, hardware/network configuration, operating system specification of the device and of the organization where the device was found installed.
Details of the forensic protocols, processes and procedures used to extract the evidence.
Hex-details of the digital products which are produced by the expert in the court as proof of the degree of originality of the evidence.
Digital transaction logs and source code presented by the expert in the court as proof of the degree of originality of the evidence.
in their forensic report. The said report is nothing but “The Certificate” that authenticates each piece of digital evidence.
PRACTICAL POSITION WHILE DEALING WITH CYBERCRIMES
Even after issuing such directions and guidelines by courts, the current situation going on while handling such cyber-crimes by the investigating agencies can be elucidated through the famous and very recent case of S. M Balaji v. State.
Brief Facts
In this case, Dr Gunaseelan (complainant) received an e-mail with derogatory contents against him and his colleagues. Moreover, the e-mail was full of insinuations and allegations of fraud. So based on the complaint filed by Dr Gunaseelan, the police registered and FIR for the offences under Sections 500 and 507 IPC and Section 66-A of the Information Technology Act, 2008 against "suspected e-mail ID: mfssurgeons@gmail.com".
Later on, the Investigating Officer filed a final report before the XI Metropolitan Magistrate, Chennai against Jayaprakash (A1) and Dr.Balaji (A2) stating there was no material evidence to add Dr Balaji as an accused. The said report was refused by Mr Abraham Lincoln, Metropolitan Magistrate and was dismissed without notice to Dr Gunaseelan. Aggrieved with the above decision, Dr Gunaseelan filed a criminal complaint before the High Court, and the court as a result set aside the order passed by the XI Metropolitan Magistrate, Chennai.
The metropolitan magistrate heard and directed further investigation under Section 156(3) Cr.P.C., since he found several lacunae like the absence of certificate under Section 65-B of the Evidence Act, 1872, etc., in the collection of evidence and in relying upon documents filed by the Investigating Officer. Further, investigation was going on. And again, the IO has added Dr Balaji as an accused based on further investigation.
The very reason for focusing our research on the above is that it is clearly evident from the above facts that there is a lot of confusion created as to how the investigation should be conducted while tackling cybercrimes. Moreover, there is a need for proper legislation and training in order to equip the investigating agencies and also to reduce the rate of cybercrimes in the country.
CONCLUSION
Since, the Internet and other information tools carried with them the concerns which were not foreseen, for example, the obstacles which may be met by the investigation officers who may not have any scientific expertise or did not have the adequate knowledge to tackle the modern situation. Moreover, the Information Technology Act, 2000 even though was revised to include various types of cybercrimes and the penalties, therefore, does not deal with all the issues which are faced by the investigation officers enforcing the said Act.
Further it is imperative to quote one of the great sayings of Bruce Schneier that “Amateurs hack systems, professionals hack people.” Thus, keeping in mind the imminent threat quoted in the preceding point, it can be summed up that there is a significant need to divulge the required legal and technical training to our law enforcement officials, including the Judiciary and the Police officials to fight the Cybercrimes and to effectively enforce cyber laws. Because of the speed at which communications technologies and computers are evolving, even experts must receive regular and frequent training in the investigation and prosecution of the high-tech case.




Comments